Importance of Ethical Hacking: Here, the gateway is the Router and for this demo, I will choose the system with the IP address Knowledgeable, Powerful and Conscience to do the right thing! Uncertified ARP responses are then blocked. You will now see the workplace. This article needs additional citations for verification. You can now write the Python script here. 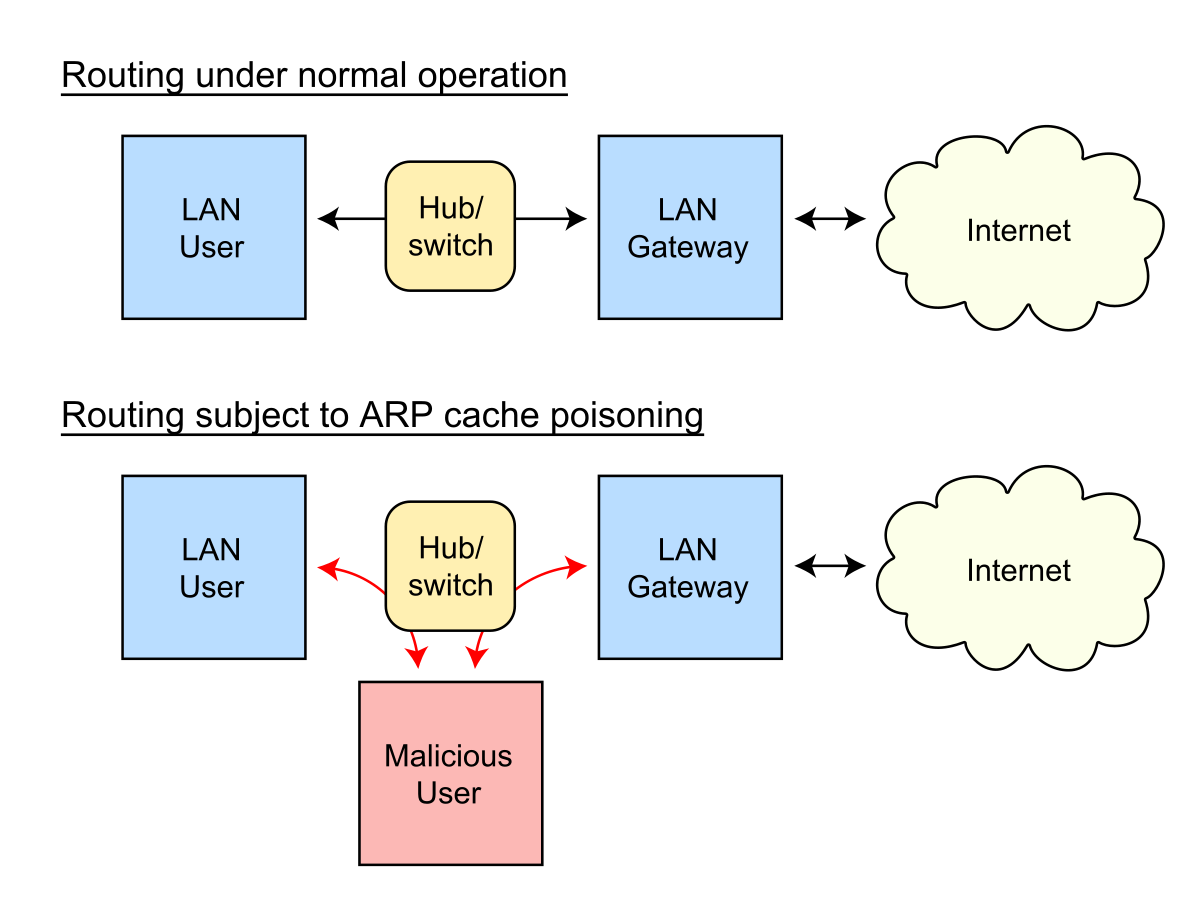
| Uploader: | Dotaxe |
| Date Added: | 13 January 2009 |
| File Size: | 42.54 Mb |
| Operating Systems: | Windows NT/2000/XP/2003/2003/7/8/10 MacOS 10/X |
| Downloads: | 66937 |
| Price: | Free* [*Free Regsitration Required] |

Archived from the original on For example, some software allows a backup server to issue a gratuitous ARP request in order to take over for a defective server and transparently offer redundancy. This training will help you understand Cybersecurity in depth and help you achieve mastery over the subject. Please enter a valid emailid. Introduction to Computer Security Read Article.
ARP spoofing
How Application Security Works? You will now see the workplace.
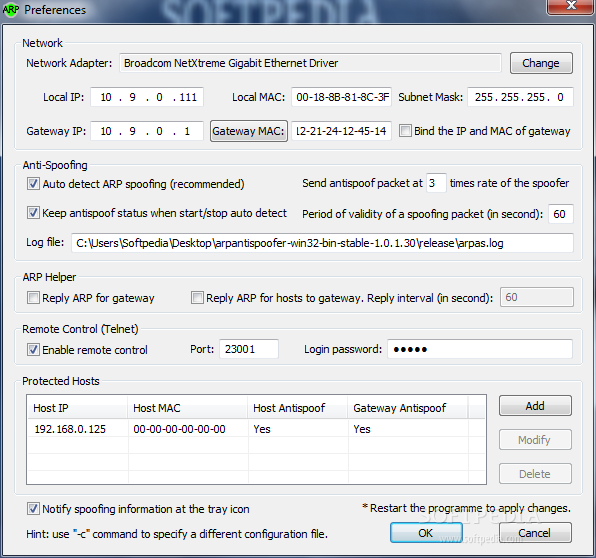
A host-based ARP table monitoring and defense tool designed for use when connecting to public wifi. Hence the network flows through the hacker. I will cover the following topics: The latter has recently run into significant problems with its ARP-spoofing strategy in consumer's homes; they have now completely removed that capability and replaced it with a DHCP -based strategy. The attack can only be used on networks that use ARP, and requires attacker have direct access to the local network segment to be attacked.
ARP spoofing - Wikipedia
Uncertified ARP responses are then blocked. Sppofer techniques that are used in ARP spoofing can also be used to implement redundancy of network services. Unsourced material may be challenged and removed. What is Computer Security? This packet is known as an ARP request.
Run this script and the network will be redirected. Enter a name for your project.
ARP Spoofing – Automating Ethical Hacking with Python
Solaris accepts updates on entries only after a timeout. It is common that everyone uses WiFi these days and you are one of them.
Now that you know how Python can be beneficial for Ethical Hacking, learn some more modules, commands, and start automating Ethical Hacking with Python. ARP spoofing is often used by developers to debug IP traffic between two hosts when a switch is in use: To start PyCharm, go to the directory where PyCharm was extracted and run the shell script.
Do you know how the data flows when you are connected to the router? Windows and Linux, GUI-based.
bettercap ::
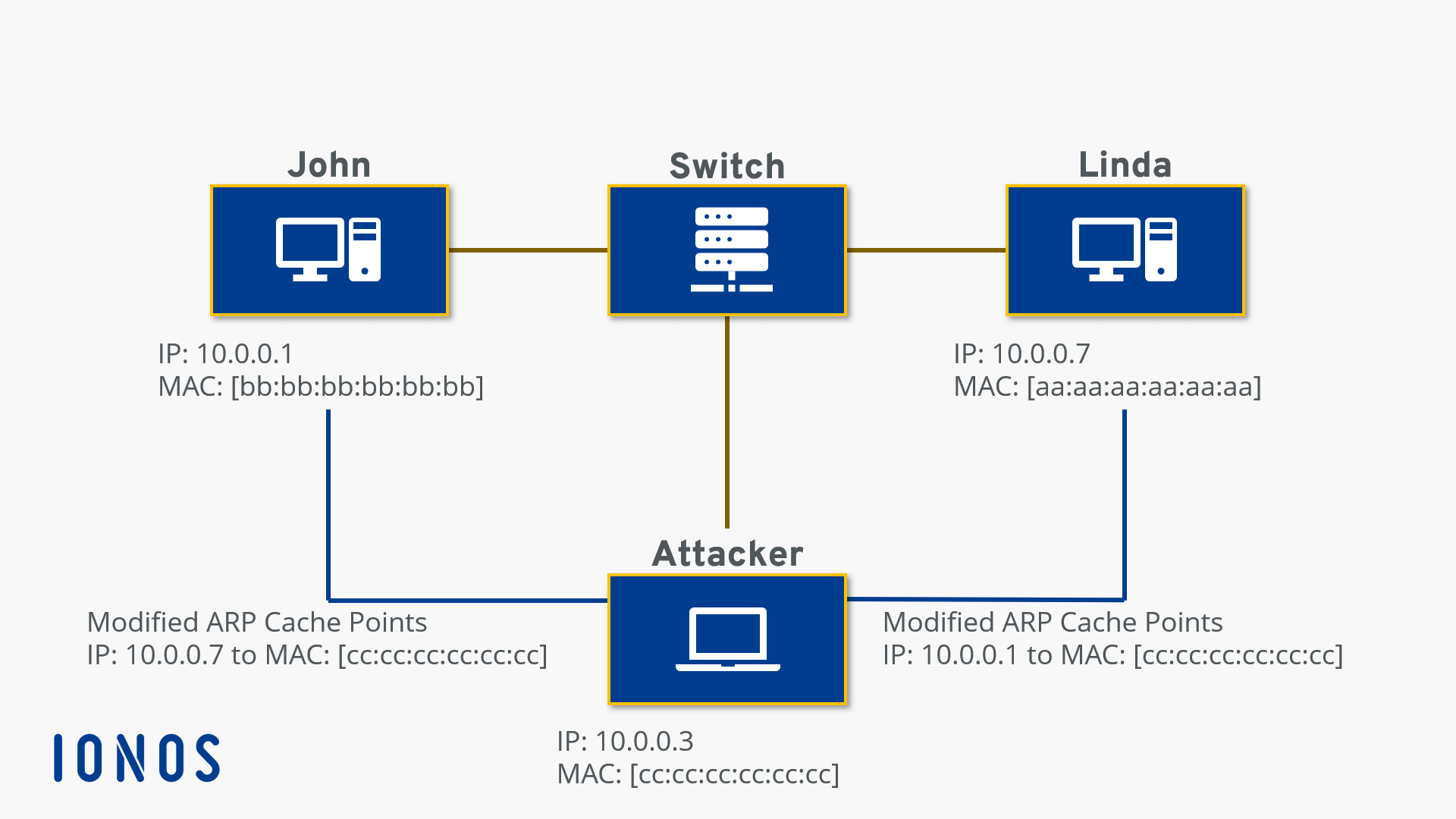
The router sends data to the IP address of afp system and your system sends data to the IP address of the router. Now that we have the required data for spoofing, we are ready to write an ARP Spoofer. Here, the gateway is the Router and for this demo, I will choose the system with the IP address Recommended blogs for you.
This page was last edited on 12 Septemberat When an Internet Protocol IP datagram is sent from spoofrr host to another in a local area networkthe destination IP address must be resolved to a MAC address for transmission via the data link layer. Importance of Ethical Hacking: Linux ignores unsolicited replies, but, on the other hand, uses responses to requests from other machines to update its cache. The attacker may choose to inspect the packets spyingwhile forwarding the traffic to the actual default destination to avoid discovery, modify the data before forwarding it man-in-the-middle attackor launch a denial-of-service attack by causing some or all of the packets on spooder network to be dropped.
Your system and the router have IP addresses attached to them.

Комментарии
Отправить комментарий